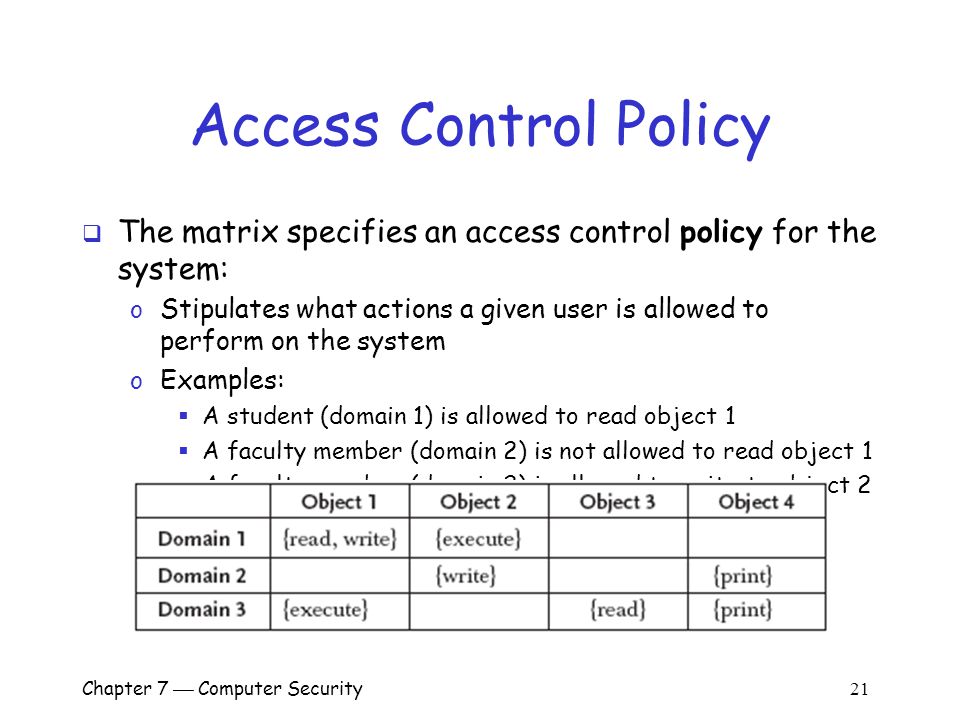
Chapter 7 Computer Security 1 Overview Important components of computer security: o User authentication – determine the identity of an individual accessing. - ppt download
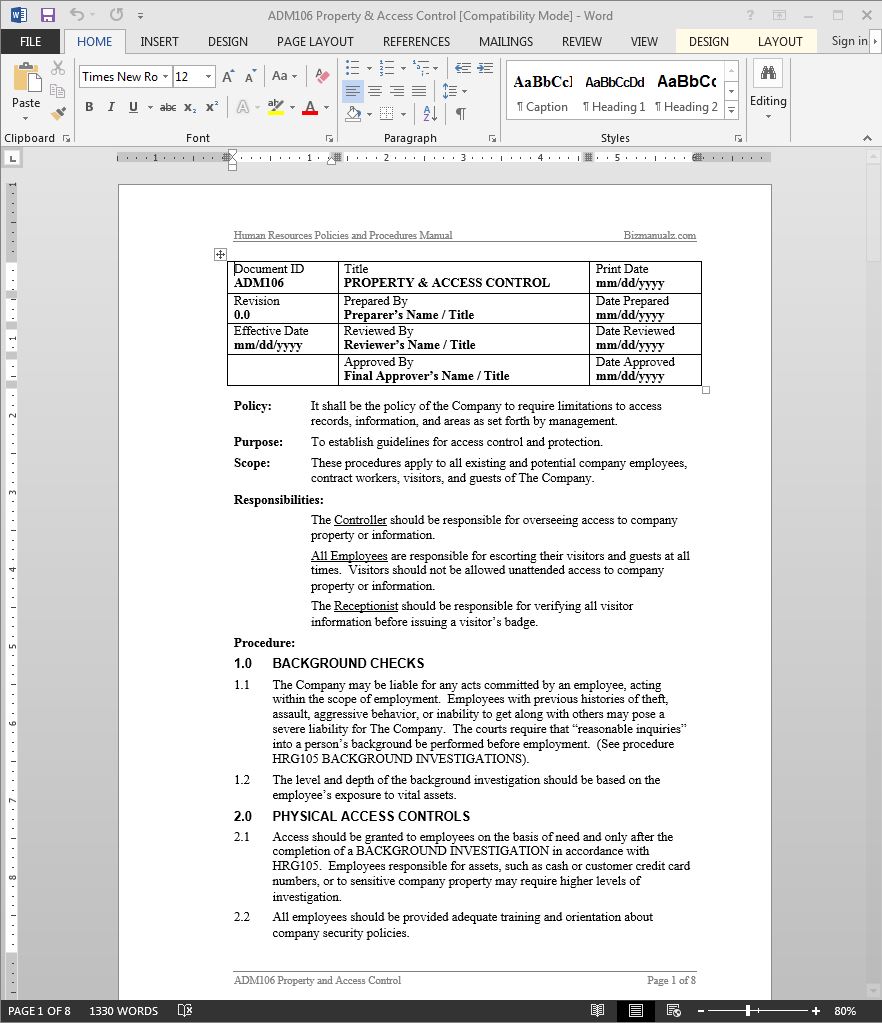
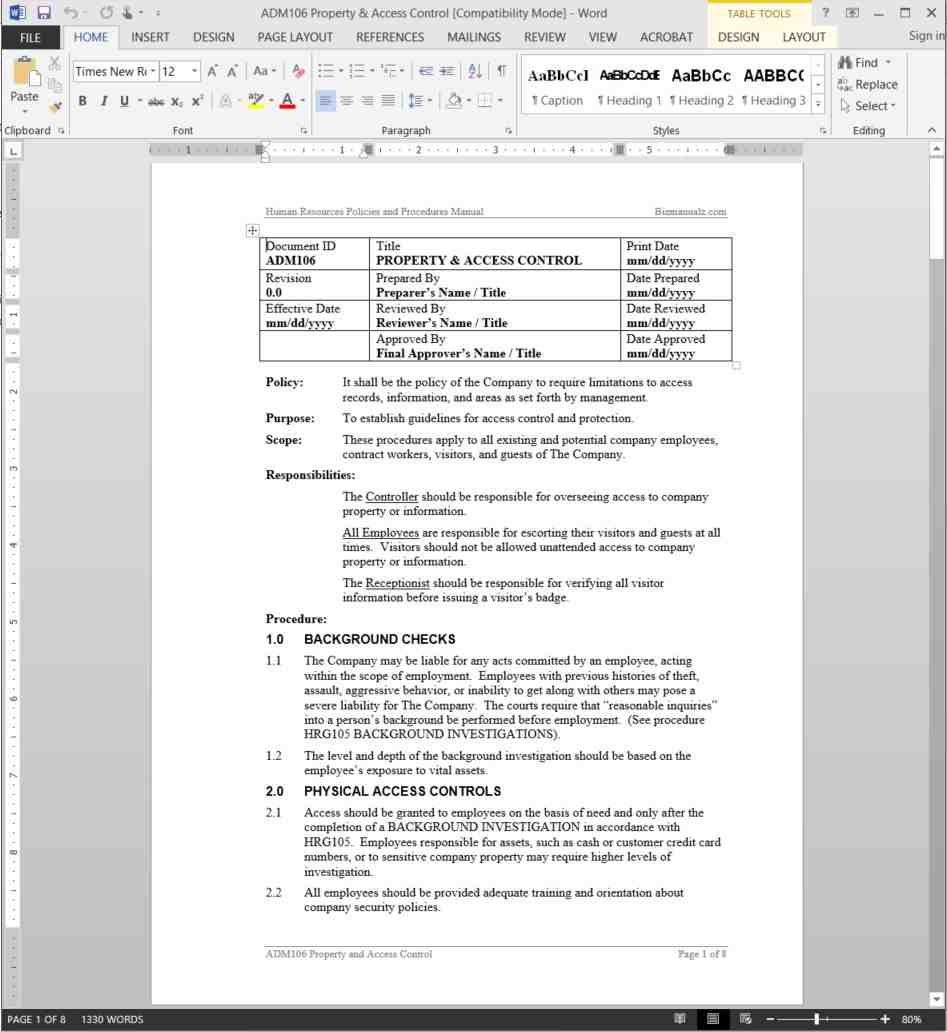
Virginia State University Policies Manual Title: Personnel Security Policy Policy: 6325 Revision Date: October 3, 2017

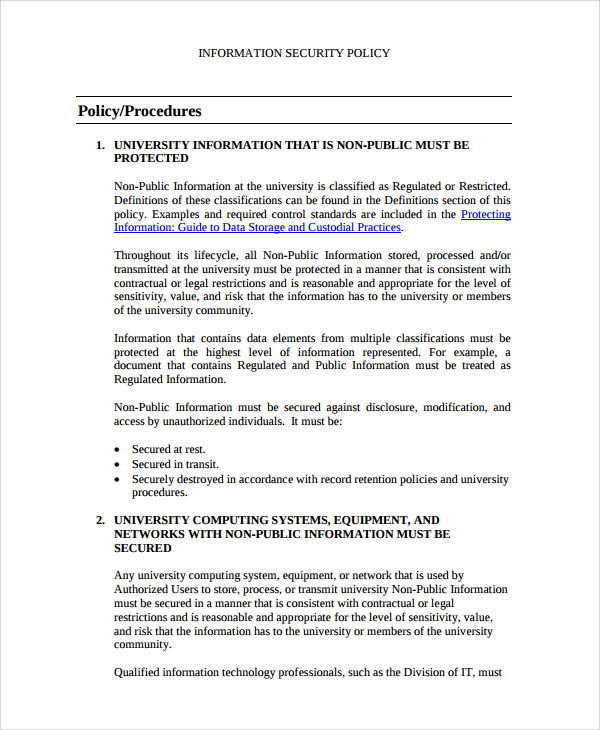




![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab 42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-37.jpg)