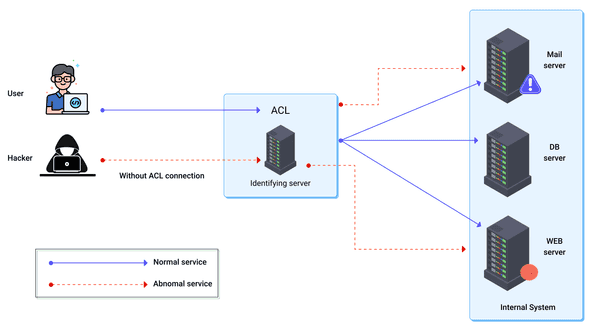
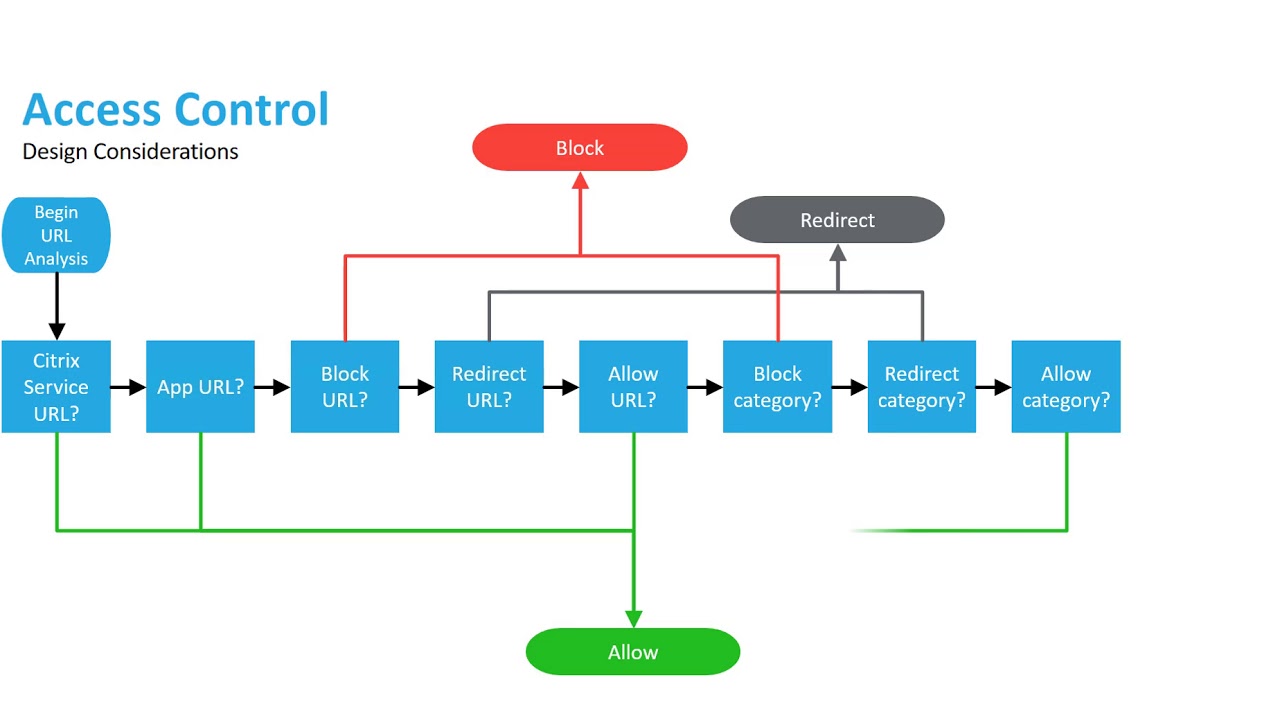
Comparison of different Access Control Mechanisms in a cloud environment. | Download Scientific Diagram

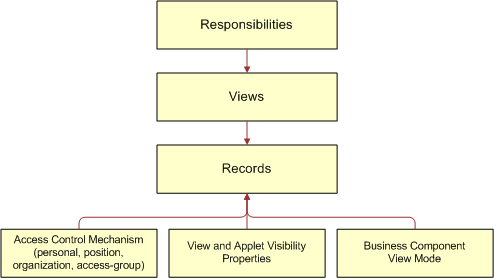
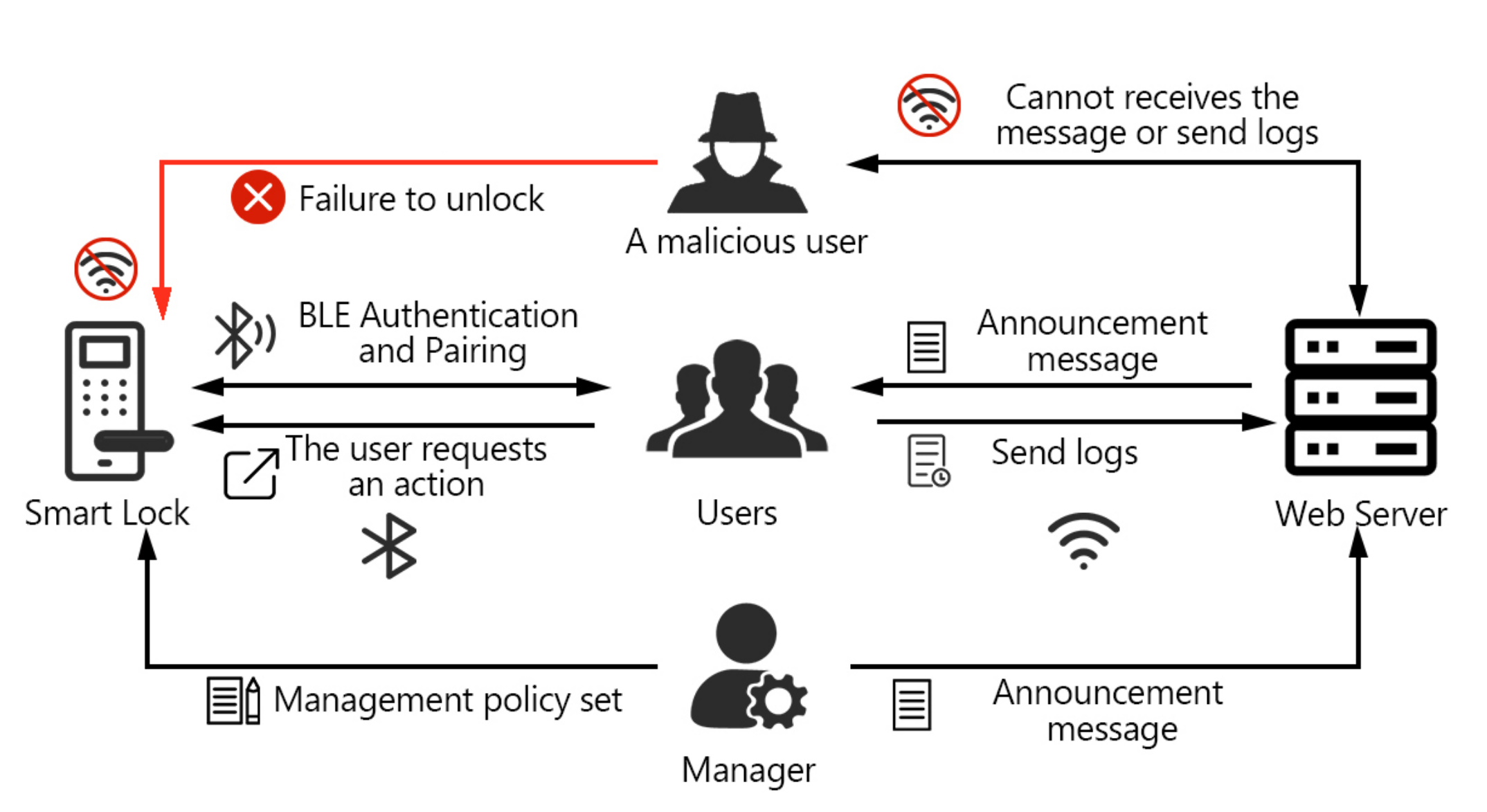
Architecture Of Access Control Mechanism In Run Time Change Management | Download Scientific Diagram

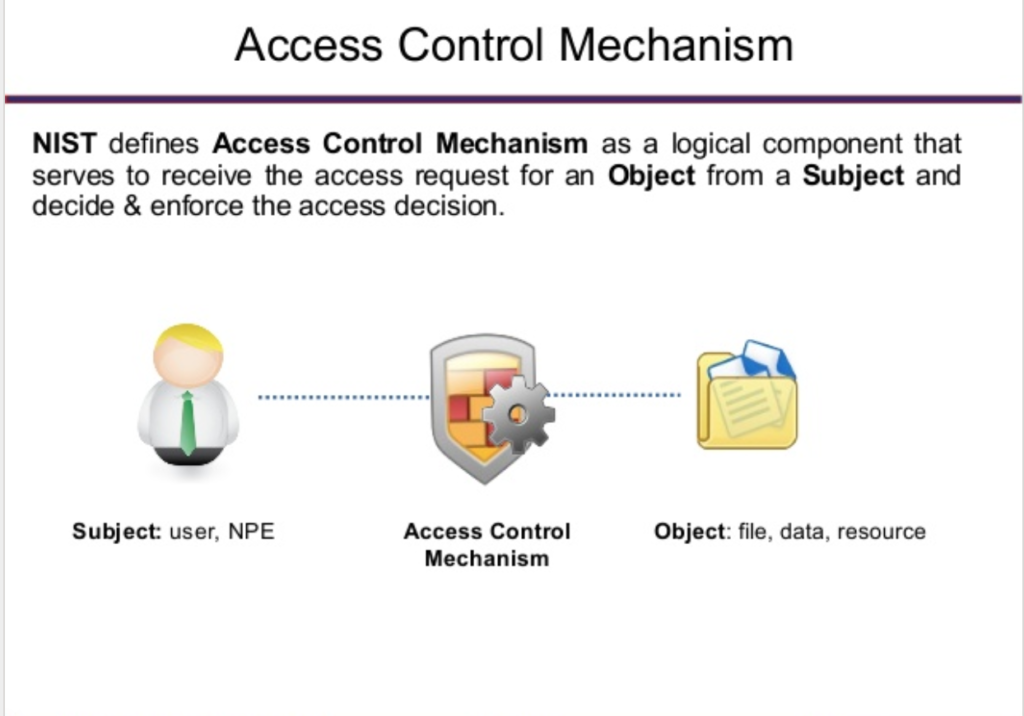
Discretionary and Non-Discretionary Access Control Policies by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

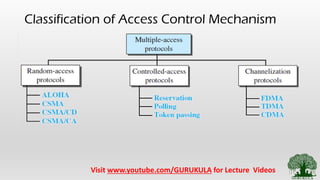
Symmetry | Free Full-Text | Permission-Based Separation of Duty in Dynamic Role-Based Access Control Model