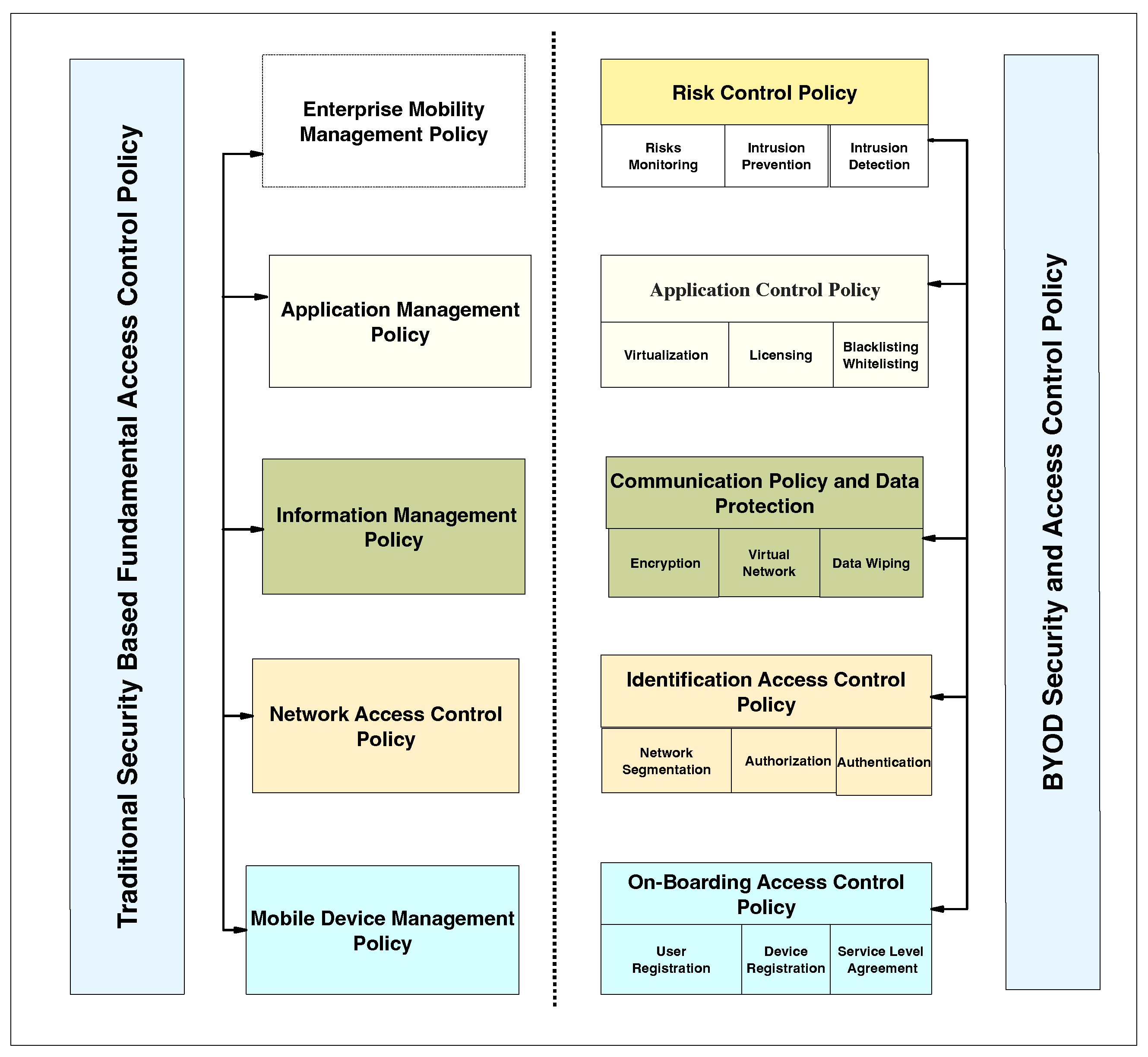
Applied Sciences | Free Full-Text | Systematic Literature Review on Security Access Control Policies and Techniques Based on Privacy Requirements in a BYOD Environment: State of the Art and Future Directions

Free Course: Information Security - Authentication and Access Control from New York University (NYU) | Class Central

Authentication and Access Control - Boonkrong, Sirapat - Ebook in inglese - EPUB3 con Adobe DRM | IBS

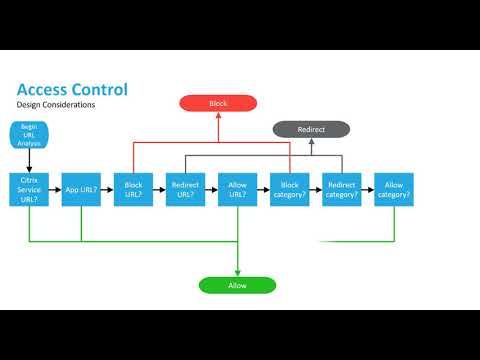
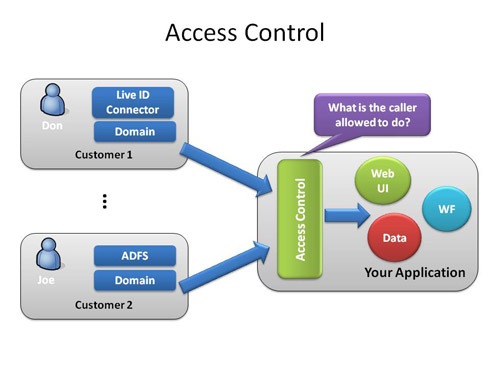
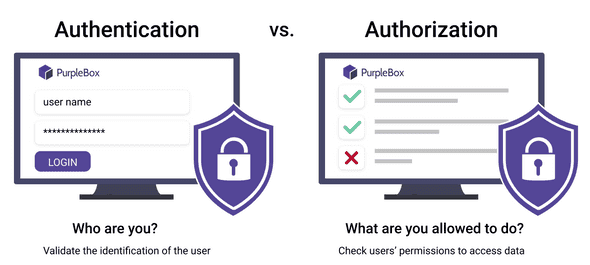
Access Control. To start off with the topic first we'll… | by Nisal Sudila | Technology Hits | Medium




![Access Control Process - Access Control and Identity Management, 3rd Edition [Book] Access Control Process - Access Control and Identity Management, 3rd Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781284198362/files/images/9781284198355_CH01_FIGF01.png)